Oct 9, 2023
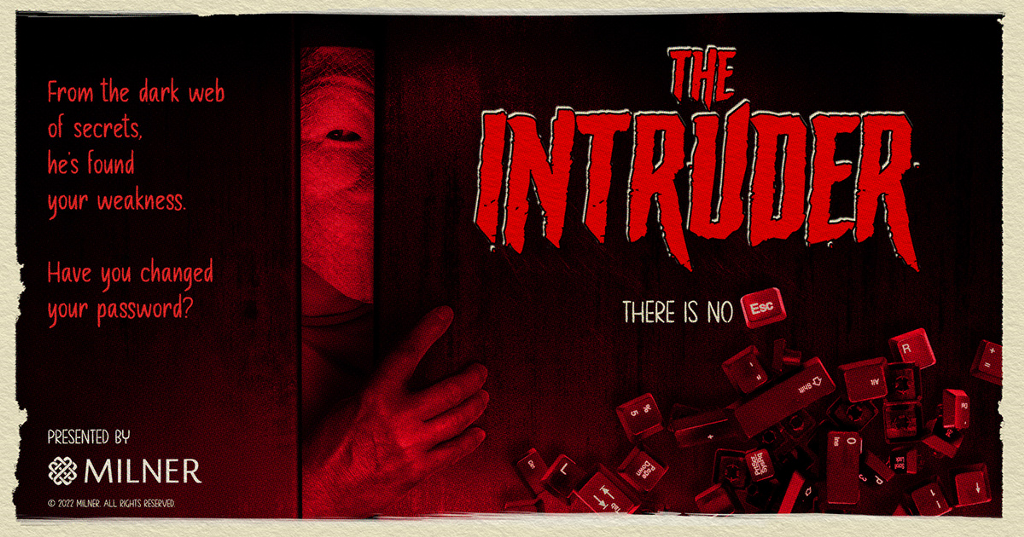
The horrors of a nightmarish Halloween attack only last a few hours in a scary movie, but in the business world, frightening cyber invasions happen daily. The scariest thing of all?
Despite the fact that data breaches can be prevented with the right security strategy, 80 percent are still caused by weak or compromised passwords.
On Halloween, many different people will come knocking on your door. How do you know who is there for good intent, or for more devilish purposes? Similarly, your IT security receives constant knocks on the door and must sort out who are the heroes, the authorized users, and who are the bad guys dressed in hero costumes every day. This is why multi-factor authentication, or MFA, has quickly become the new norm for authenticating accounts and keeping data secure.
Multi-factor authentication (MFA) is an authentication method that requires users to provide two or more points of verification to gain access to data via applications, accounts, or other resources. Rather than relying on a static, often user-generated, username and password, MFA methods call for at least one additional verification factor, which makes it more challenging for cybercriminals to breach secure data.
“Something you know, something you have, and something you are,” can sound like an ominous line from a classic horror film. Instead, it speaks to how any multi-factor authentication method will employ at least one of these three elements: knowledge, possession, and inherence. Knowledge refers to something you must know, possession refers to something that you have, and inherence refers to parts of your identity. So for example, some methods of authentication will call for a PIN or code—or knowledge—to grant secure access. Other methods might require the use of your cell phone (possession) or even your fingerprint (inherence).
In 2021, Google, the most widely used email service to date, announced that two-factor authentication would become mandatory for 150 million users. Despite this, however nearly a year later, studies have found that nearly half the companies surveyed still do not use MFA, though 30 percent of these companies plan to acquire an MFA solution within a year. Now is the time to shift to user-friendly MFA to make sure you’re letting the good ones in and the goblins out. If you’re interested in ensuring that your organization’s password practices measure up to today’s new standard for authentication, grade yourself using our Password Report Card.
Though Google has standardized its own method of two-step verification, there are multiple methods of MFA that your organization can employ to keep your data safe. Some are more secure than others.
Like the scariest of Halloween tricks, flaws in configuration and other errors can leave room for well-costumed imposters to break through MFA security measures. This is why hundreds of organizations, large and small, partner with Milner’s managed IT team to ensure that their organization’s data remains secure, even as cybercriminals become better at impersonating superheroes, as well as regular employees. For more tips on how to secure your passwords, download our password report card or reach out to our team to find out how we can help you keep your organization’s data secure.
